Houston, We Have a Problem
On April 2, 2018, the first Chinese space station – Tiangong-1 – came crashing down to earth. Headlines across the world stoked panic and alarm, and astronomers attempted to predict where the 9.5 tonne object would strike. This is not the first such object to threaten damage and destruction, and nor will it be the last.
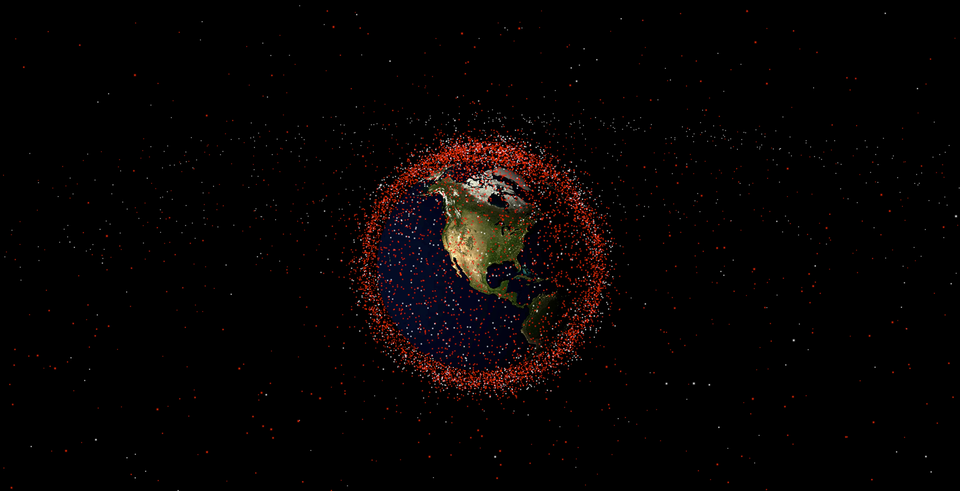
Since the beginning of space exploration, countries have raced to put objects into Earth’s orbit. As a result, there are objects in space right now providing us with telecommunications, GPS services, weather tracking and contributing to science in ways we can only imagine. But after years of being treated as international landfill, space has become increasingly more congested.
There are over 14,000 objects in space that are actually junk – fragments of spacecraft, old boosters, and forgotten satellites – no longer serving any functional purpose. Not only are they junk, but they are dangerous pieces of junk, travelling much faster than a speeding bullet at 28,000 kilometres per hour.
Businesses today have raced to launch data into orbit around the business in a way that echoes this rising problem of space debris. This is in part thanks to the arrival of the increase in cloud adoption and file sharing – which has seen employees take data out of structured systems and store it into cloud and network-based storage because it is convenient for their immediate job function.
Whether it's a presentation on SharePoint or a spreadsheet on Box, up to 80% of enterprise data is on the move, being downloaded, accessed, and shared outside of IT’s purview. This data is commonly called ‘unstructured data’ and it is a huge area of exposure for organisations today.
The scary part of this is how much of this data is sensitive. Credit card information, healthcare records, and financial data is all on the move, orbiting organisations despite the increasing risk of cyber-attack.
Even scarier? Most organisations have no idea where this unstructured data lives, what lies within that data, or who owns it. And this is the type of data that adversaries need to potentially hold an organisation, or worse, their customers, to ransom.
When thinking about data orbiting our business, we must think of it like the satellites and other objects orbiting the earth – the majority of it is dangerous, has most likely been abandoned, and is not serving a purpose. This is a challenge the international community has been tackling since it first launched, and it’s time for IT teams to do the same.
Since the beginning of space flight, nations collectively created a database capturing all relevant data about the objects being launched into space – dimensions, weight, mission, launch speed, trajectory – to fully understand what was out there. However, it quickly became apparent that there were disparities between what should be (what was logged into the database) and what actually was launched into space.
To accurately know what was out there, governments developed and deployed laser telescopes to provide ultimate visibility and accountability into this orbiting junk for scientists across the globe.
Much like the space agency and its laser satellites, organisations must seek to discover where their sensitive data resides, who has access to it and what they are doing with that data. But this is not as easy as it sounds in the enterprise, as the user frontier is also changing, adding another layer of complexity to the situation.
That is, who, or rather what organisations consider an identity has evolved to include employees, contractors, partners, and more increasingly, software bots (which, like humans, are accessing data and making decisions based on it).
The international community doesn’t just rely on satellites to understand the objects in Earth’s orbit – it has highly trained physicists determining the responsibility of objects based on their observed trajectory. This is a practice that enterprises need to understand too, as thanks to the huge number of applications entering the business, it’s not always obvious where data has come from, where it resides or who owns it.
Visibility into the environment — knowing what data is out there and who put it there – allows organisations to determine the original actor responsible for an objects’ creation, and shows how they can establish owners for the sensitive data that is found. This provides a chain of responsibility for review, persistent protection and clean-up of sensitive data usage.
This challenge of discovering and protecting an organisation’s sensitive data stored in files is one of the new frontiers of identity governance. Organisations are seeking a way to discover where this data resides and put controls in place to protect it, and the best way to do that is by governing access to this data in the same way they govern access to critical applications.
Extending identity governance to data stored in files helps organisations answer the questions of who has access to what data, who should have access to it and how that access is being used. By building on the lessons learned from sixty years of space debris management, organisations can govern the new frontier of data stored in files, and at the same time, rapidly realise that the path to a more secure enterprise isn’t actually rocket science after all.